By Douglas Borthwick · March 16, 2026
And no two fingerprints are alike.
By Douglas Borthwick · March 16, 2026
I want to tell you something that has nothing to do with smart contracts, gas fees, or middleware architecture. I want to tell you about a door that only opens for you, and why that changes everything.
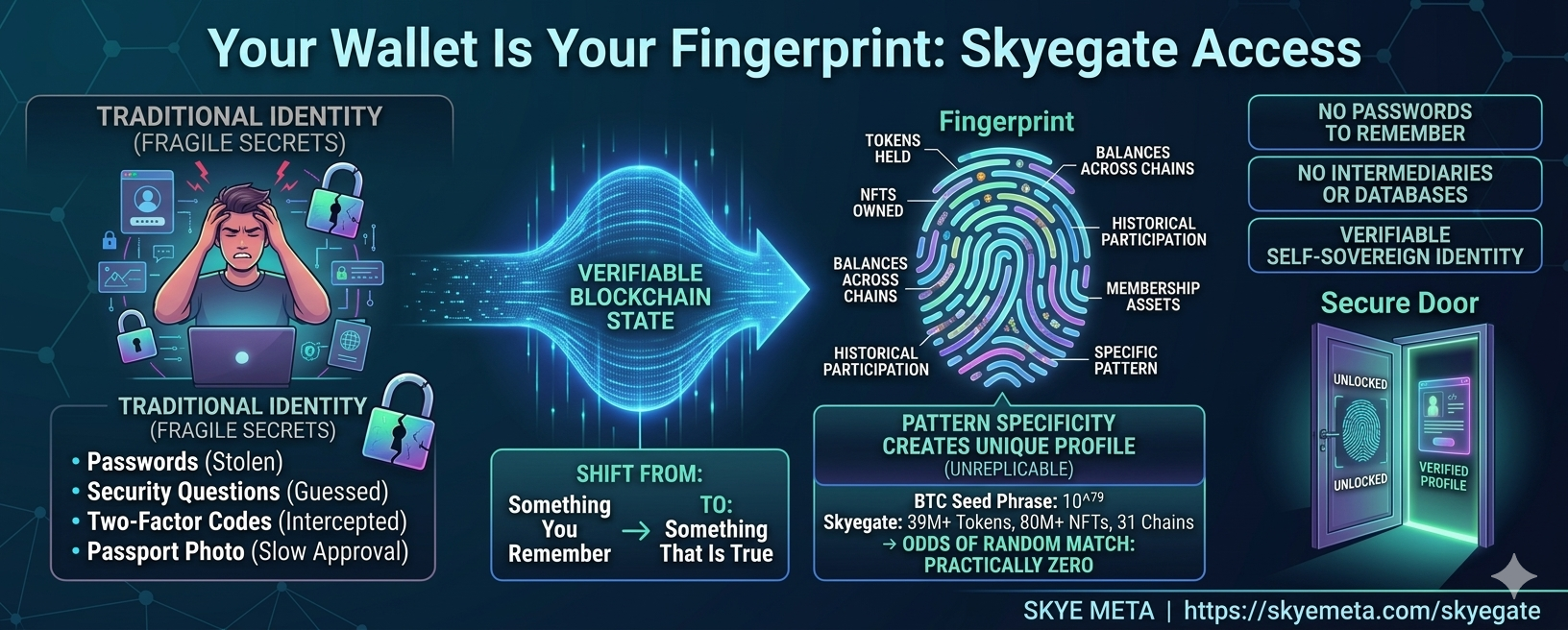
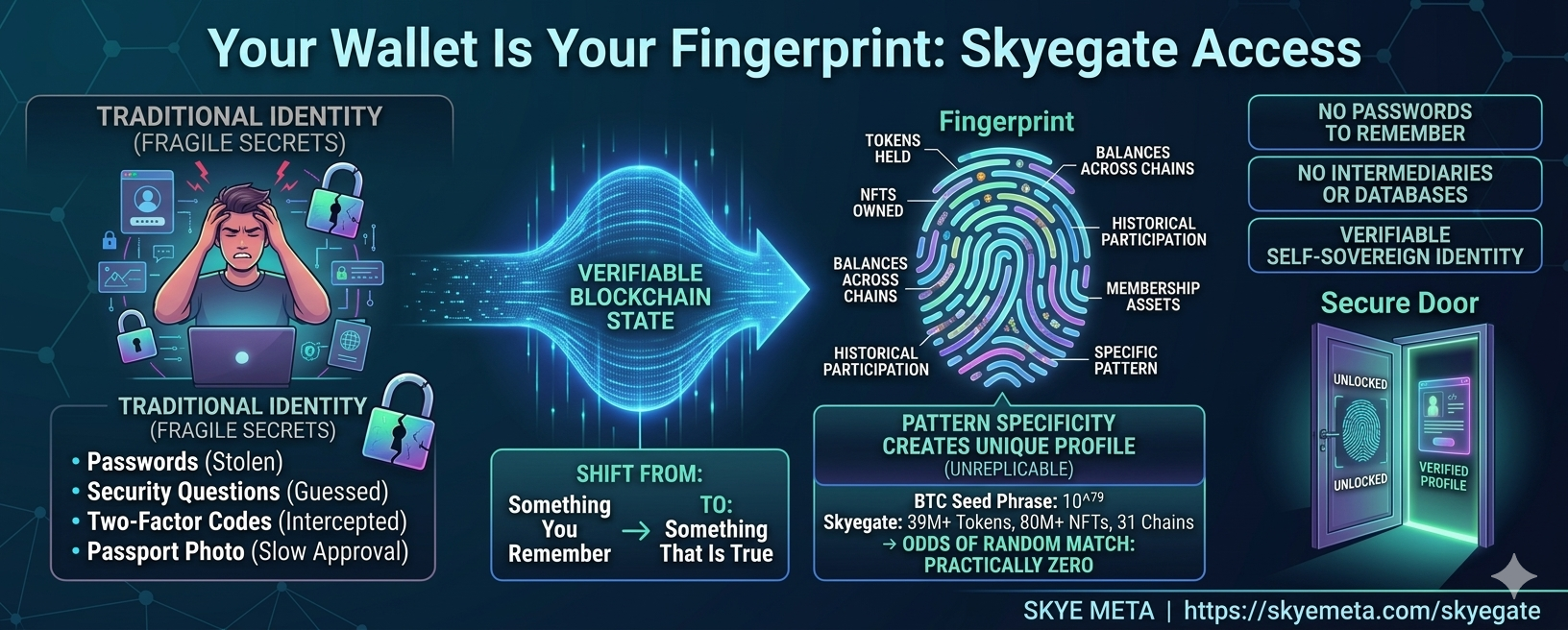
Think about the last time you proved who you were online. You typed a password someone told you to create, answered a security question about your mother's maiden name, waited for a six-digit code to arrive on your phone, or uploaded a photo of your passport and waited three days for someone somewhere to approve it. Every one of those systems exists to solve the same problem: how does a system know it's really you?
For fifty years we have tried to solve that with the same tools. Passwords, security questions, two-factor codes, identity checks. They work most of the time. But they all rely on something fragile — a secret that can be stolen, guessed, leaked, or reset. What if identity online didn't depend on something you remembered? What if it depended on something that was simply true?
Here is the idea at the heart of SkyeGate.
Your on-chain wallet profile — the combination of tokens you hold, NFTs you own, and the chains you hold them on — forms a pattern that is extraordinarily difficult to replicate. In that sense, it behaves like a fingerprint. Not because it proves who you are in the real world, but because the exact pattern is so specific it is unlikely to exist anywhere else.
A human fingerprint has roughly 35 to 50 distinguishing features, and forensic science typically needs only 12 matching points to establish identity beyond reasonable doubt. A SkyeGate profile checks 10 different on-chain conditions: tokens held, NFTs owned, balances across chains, membership assets, historical participation. Each condition is simple on its own. Together, they become something else entirely.
To understand the scale of this, consider Bitcoin. A Bitcoin wallet is protected by a 24-word seed phrase, and the number of possible combinations is roughly 10⁷⁹, a number larger than the atoms in the observable universe. That is why Bitcoin seed phrases are considered effectively unbreakable.
SkyeGate's combination space, drawn across 39 million tokens, 80 million NFTs, and 31 blockchains, is orders of magnitude beyond that. The odds of two wallets randomly matching the exact same profile become, for practical purposes, zero. There is no brute-force attack. There is no rainbow table. There is no social engineering a system that has no password to steal.
Imagine a simple website. The page is public and the URL is not secret, but the content only appears if your wallet matches a specific on-chain profile. No password, no login form, no account reset.
Here is what actually happens when someone connects their wallet. SkyeGate is powered by InsumerAPI, the verification infrastructure built by The Insumer Model™. InsumerAPI reads the blockchain state directly across 31 chains, then signs the result using ECDSA — Elliptic Curve Digital Signature Algorithm — the same cryptographic standard that secures blockchain transactions themselves. What comes back is not simply a yes or a no. It is a cryptographically signed attestation of the result, one that can be independently verified by anyone against a public key, with no exposure of the visitor's actual balances or holdings. Blockchain state in, signed credential out.
SkyeGate only releases the content from the server after that signed attestation passes. Before it passes, the content is not in the page source, not in the DOM, not visible in network traffic. It does not exist on the browser side at all.
It is worth being precise here, because token-gating already exists and SkyeGate is something different. Conventional token-gating works like a club membership: hold this NFT and you can enter. That is a shared key. Everyone who holds the token can open the same door.
SkyeGate checks a precise combination of on-chain conditions rather than a single asset. The creator of the gate decides how specific that combination is. It can be broad enough to admit an entire community of holders. It can be narrow enough that only a handful of wallets in the world qualify. Or it can be precise enough that only one person on earth can open it. The same mechanism, dialed from a million to one.
That is what makes it fundamentally different from anything that exists today. Access is not binary — open or closed, member or not. It is tunable. A company can speak to all its token holders, or only to those above a certain threshold, or to a single counterparty, using exactly the same system.
Most access control on the internet today falls into three categories. Passwords are something you know. Two-factor codes are something you receive. KYC systems are something you submit. All of them rely on databases, intermediaries, and secrets that can be compromised, breached, or subpoenaed.
SkyeGate introduces a fundamentally different option. Access based on verifiable blockchain state, signed cryptographically by InsumerAPI, and verified independently by anyone who wants to check it. No passwords to remember, no credentials stored on a server, no shared keys to leak, and no third party that has to be trusted to tell the truth about the result. The signed attestation speaks for itself.
Once you understand the mechanism, the use cases become obvious. An investment fund can publish a report visible only to wallets holding verified LP tokens — that's SkyeGate. A brand can open a product drop to an entire community of collectors, or offer wallet-verified discounts that can't be shared or leaked — that's SkyeWoo. Two AI agents can verify each other's wallet holdings before exchanging sensitive data — that's AgentTalk. A board can speak directly to its shareholders with no login, no platform, and no intermediary standing between them. The internet already has the content. Blockchains now provide the keys.
People talk a lot about self-sovereign identity, but most systems still rely on a platform somewhere — a login provider, a database, an identity service that someone else controls and someone else can revoke. SkyeGate, powered by The Insumer Model™'s InsumerAPI, removes that dependency entirely. It reads blockchain state directly, signs the result cryptographically, and returns a verifiable credential. It does not require anyone to maintain a list. It does not require anyone to be trusted. It simply checks what is provably true on-chain, signs that truth, and lets you verify the signature yourself.
The most important thing about SkyeGate is not the architecture. It is the idea. Somewhere on the internet, there could be a page that opens for an entire community, or for a handful of people, or for exactly one wallet in the world. Not because someone issued a password, and not because a platform granted permission, but because of who they are on-chain.
That door now exists. skyemeta.com/skyegate
To understand the underlying primitive, read What Is Wallet Verification? Or see the full product stack — content, commerce, and agents, all powered by the same verification engine.